
Change Management Starts with the People
May 15, 2024In April, we provided our readers with a framework for the new Chief Experience Officers emerging in the workforce. However, if it...Read More
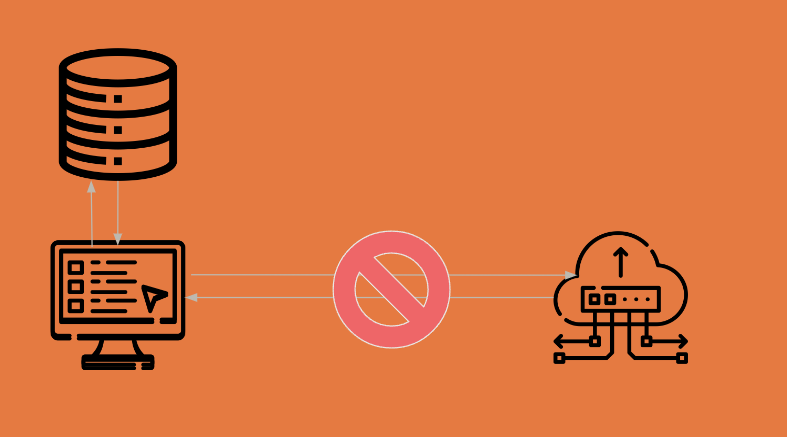
Navigating Remote Assistance in Air-Gapped Environments: Tips from a Software Consultant
April 30, 2024In the world of software consulting and remote support, especially within air-gapped environments, the importance of not just having solutions...Read More

First Day Insights: A Chief Experience Officer’s Guide to Balancing Specialization and Integration
April 17, 2024The first day as a Chief Experience Officer involves dissecting the existing tech stack and charting a path to enrich...Read More

Enhancing Government Efficiency: Kinetic Data’s Role in Modernization through Webform-to-PDF Conversion
April 9, 2024At Kinetic Data, we’re keenly aware of the federal government’s commitment to modernization and digitization, a mission we actively support...Read More

Balancing Resource Sharing in Multi-tenant Architectures with Single-tenant Services
March 20, 2024Architecting multi-tenant solutions, especially when integrating single-tenant services, poses unique challenges that require careful planning and design. This article delves...Read More

Why Elixir May Be Kinetic Data’s Future
March 14, 2024Why did we choose Elixir as one of our primary development tools? Several factors went into this decision. It may...Read More

Bright Starts: Kinetic Data’s Guide to Successful Project Kickoffs
March 7, 2024Like flipping on a lightbulb to dispel the darkness and illuminate a room, a project manager must light the way...Read More

Navigating Post-Project Waters: How Kinetic Data Takes Support the Extra Mile
February 26, 2024Navigating the post-project waters is a critical phase in any software implementation. At Kinetic Data, we understand the journey doesn’t...Read More
Simulating Data Connections with Placeholder APIs
February 21, 2024Kinetic Data provides the flexibility to allow development throughout design, by enabling you to set up a simulated data source....Read More
Try the Kinetic Platform Today.
When you're ready to learn how Kinetic Data can help you achieve better business outcomes, we're here to answer your questions.